The digital battlefield is evolving faster than ever, and 2026 promises to be a pivotal year in the ongoing war between cybercriminals and defenders. As our lives become increasingly intertwined with technology—from AI assistants managing our schedules to smart devices controlling our homes—the attack surface for malicious actors expands exponentially.
Here’s the uncomfortable truth: cybercrime damages are projected to exceed $10.5 trillion annually by 2026, making it more profitable than the global trade of all illegal drugs combined. Meanwhile, the cybersecurity talent shortage continues to worsen, with an estimated 3.5 million unfilled positions worldwide. Organizations aren’t just fighting sophisticated threats—they’re fighting them understaffed and often unprepared.
But this article isn’t about doom and gloom. It’s about preparation, awareness, and staying ahead of emerging threats. Whether you’re a business leader responsible for protecting customer data, an IT professional on the front lines, or simply someone who wants to understand the cyber risks shaping our future, this comprehensive guide reveals the cybersecurity trends that will define 2026—and what you need to do about them right now.
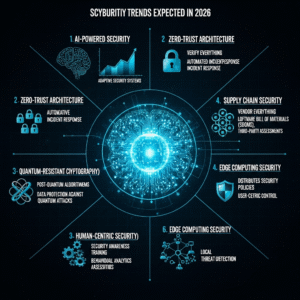
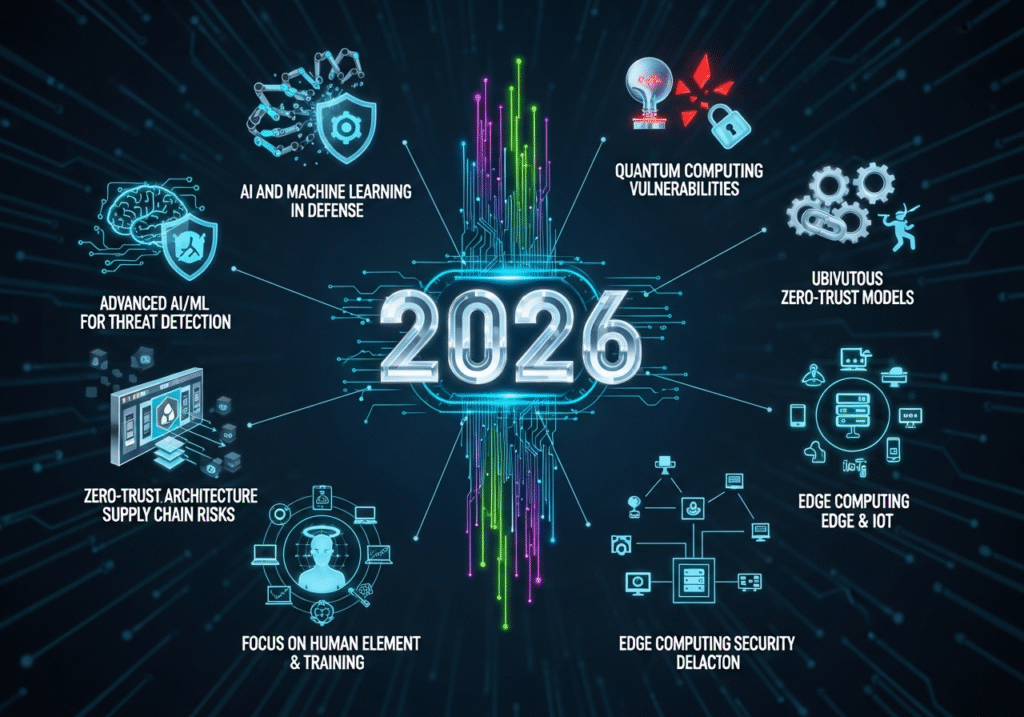
AI-Powered Cyberattacks Reach Maturity
The Democratization of Sophisticated Attacks
Artificial intelligence has become the great equalizer in cybercrime. What once required specialized technical knowledge and months of preparation can now be accomplished by relatively unsophisticated actors using AI tools.
Cybercriminals in 2026 leverage generative AI to create polymorphic malware that continuously rewrites its own code, evading signature-based detection systems that have protected networks for decades. Each instance of the malware looks different, making traditional antivirus solutions nearly useless.
AI-powered phishing campaigns have reached disturbing levels of sophistication. These attacks analyze social media profiles, writing styles, and communication patterns to generate personalized messages virtually indistinguishable from legitimate correspondence. The generic “Nigerian prince” emails of the past have evolved into targeted communications that reference specific projects, colleagues, and internal information.
Deepfake technology enables impersonation attacks that bypass voice and video authentication. In documented cases, criminals have already stolen millions by impersonating CEOs in video calls, instructing finance teams to transfer funds. By 2026, distinguishing real from fake in real-time communication becomes increasingly challenging without specialized verification systems.
AI as the Shield
Fortunately, AI-powered defense systems are advancing equally rapidly. Machine learning models now detect anomalies in network traffic, user behavior, and system access patterns that human analysts would never spot.
Behavioral analytics create detailed profiles of normal user and system behavior. When deviations occur—an accountant suddenly accessing engineering files at 3 AM, for example—security systems flag or automatically block the suspicious activity before damage occurs.
Automated threat hunting continuously scans environments for indicators of compromise, examining millions of events to identify the subtle patterns that signal intrusions. This proactive approach finds threats before they fully materialize, fundamentally shifting from reactive incident response to preventive security.
Organizations succeeding in 2026 don’t choose between AI attackers and AI defenders—they integrate AI throughout their security stack and accept that manual approaches simply can’t match the speed and scale of modern threats.
The Quantum Computing Threat Looms Large
Why Current Encryption Is at Risk
Quantum computing represents both tremendous opportunity and existential risk to cybersecurity. While still emerging, quantum computers possess capabilities that will render current encryption methods obsolete.
The encryption protecting your bank accounts, medical records, business secrets, and government communications relies on mathematical problems that classical computers can’t solve in any reasonable timeframe. A quantum computer, however, can break RSA and ECC encryption—the backbone of internet security—in hours or even minutes.
“Harvest now, decrypt later” attacks are already occurring. Sophisticated adversaries intercept and store encrypted data today, knowing they’ll be able to decrypt it once quantum computers become sufficiently powerful. If your organization handles sensitive information with long-term value—medical records, trade secrets, personal information, classified data—that information is already at risk.
The Race to Post-Quantum Cryptography
Organizations in 2026 face critical deadlines for quantum-resistant encryption implementation. The National Institute of Standards and Technology (NIST) has published post-quantum cryptographic standards, but migration represents a monumental undertaking.
Post-quantum cryptography (PQC) uses mathematical approaches believed to be resistant to quantum attacks. However, implementing PQC isn’t as simple as flipping a switch—it requires:
- Comprehensive inventory of all systems using current encryption
- Compatibility testing with existing infrastructure
- Performance optimization (PQC algorithms are often more resource-intensive)
- Gradual migration strategies to maintain security during transition
- Long-term monitoring as quantum computing capabilities evolve
Crypto-agility—the ability to quickly swap cryptographic algorithms—becomes a fundamental architectural requirement. Organizations can’t predict exactly when quantum computers will threaten current encryption, so they need infrastructure capable of rapidly adopting new cryptographic methods as threats emerge.
The organizations taking action in 2026 will be protected. Those waiting will face catastrophic compromises when quantum computers inevitably mature.
Zero Trust Architecture Becomes the Standard
The End of “Trust But Verify”
The traditional security model—trusted internal networks and untrusted external ones—died with cloud computing and remote work. Organizations in 2026 finally accept this reality and embrace zero trust architecture comprehensively.
Zero trust operates on a simple principle: never trust, always verify. Every access request requires authentication and authorization regardless of whether it originates inside or outside the network perimeter. Location, previous authentication, and network connection grant no implicit trust.
This shift responds to the collapse of meaningful network boundaries. When employees work from home, applications run in cloud environments, and partners access systems directly, the concept of a trusted internal network becomes meaningless and dangerous.
Implementing Zero Trust in Practice
Microsegmentation divides networks into small, isolated zones. Even if attackers breach one segment, they can’t move laterally across the environment without repeatedly authenticating and being authorized for each resource.
Identity-based access control replaces network-based permissions. Users receive access based on verified identity and specific role requirements, not their network location. Access grants are temporary and continuously re-validated.
Least privilege access ensures users and systems receive only the minimum permissions necessary for their specific tasks. An employee who needs to view customer data shouldn’t have permission to export entire databases, even if they’re an authenticated user.
Continuous monitoring and analytics verify that authenticated users behave appropriately. Anomalous behavior triggers immediate investigation or automated restriction regardless of valid credentials.
Organizations implementing zero trust in 2026 report significant reductions in breach impact. Even when attacks succeed initially, lateral movement becomes nearly impossible, containing damage before it spreads.
Ransomware Evolves and Escalates
Targeting Operational Technology
Ransomware attacks in 2026 increasingly target operational technology (OT) and industrial control systems rather than just IT networks. These attacks threaten physical infrastructure—manufacturing plants, power grids, water treatment facilities, transportation systems.
The consequences extend far beyond encrypted files and ransom demands. Disrupting operational technology can endanger lives, damage expensive physical equipment, and create cascading failures across critical infrastructure networks.
Triple extortion tactics have become standard. Attackers first encrypt data, then threaten to leak it publicly, and finally threaten to attack customers, partners, or suppliers if ransoms aren’t paid. Some attacks now include DDoS attacks on victim organizations during ransom negotiations as additional pressure.
Ransomware-as-a-Service Proliferation
RaaS platforms have industrialized cybercrime. Criminal organizations provide the malware, payment infrastructure, and victim targeting while affiliates execute attacks for a percentage of ransoms. This model dramatically lowers barriers to entry, enabling less sophisticated criminals to launch devastating attacks.
The business model has proven remarkably resilient. Law enforcement takes down one operation, and three more emerge. The economic incentives—ransoms frequently reaching millions of dollars—ensure continuous supply of both platform operators and affiliates.
Defense Strategies That Work
Organizations successfully defending against ransomware in 2026 implement layered defense strategies:
- Immutable backups stored offline and verified regularly ensure recovery without paying ransoms
- Network segmentation prevents ransomware from spreading if it breaches one system
- Endpoint detection and response (EDR) identifies and stops ransomware before encryption begins
- Email filtering and user training blocks initial access vectors used in most attacks
- Incident response plans tested regularly enable rapid, coordinated response when attacks occur
Critically, organizations recognize that prevention, while essential, isn’t sufficient. The question isn’t if you’ll face a ransomware attack but when and how effectively you’ll respond.
Supply Chain Security Becomes Critical
The Ripple Effects of Third-Party Compromises
Supply chain attacks exploit the weakest link in interconnected business ecosystems. Attackers compromise a software vendor, service provider, or supplier, then use that access to breach dozens or thousands of downstream customers.
The SolarWinds attack demonstrated this threat’s severity, but it was just the beginning. In 2026, supply chain compromises have become one of the most effective attack vectors because organizations often trust vendors more than they should.
Software supply chain attacks inject malicious code into legitimate applications during development or distribution. When customers download and install the compromised software, they unknowingly grant attackers access to their environments.
Hardware supply chain attacks embed backdoors or malicious components in devices during manufacturing. Organizations receive compromised equipment that appears legitimate but contains hidden access mechanisms for adversaries.
Due Diligence and Continuous Monitoring
Vendor risk management programs in 2026 go far beyond questionnaires and occasional audits. Organizations implement:
- Continuous security monitoring of vendor access to their environments
- Software composition analysis identifying all components and dependencies in applications
- Regular security assessments of critical vendors with remediation requirements
- Contractual security requirements with financial penalties for breaches
- Software bill of materials (SBOM) tracking for all applications, enabling rapid response when vulnerabilities emerge
Zero trust principles apply equally to vendor access. Third parties receive only necessary permissions, access is continuously monitored, and trust is never assumed based on contractual relationships.
The harsh reality of 2026: you’re responsible for security failures of your vendors. Customers, regulators, and courts increasingly reject “our vendor was compromised” as an acceptable excuse for data breaches.
Privacy Regulations Expand Globally
The Compliance Complexity Crisis
Data privacy regulations in 2026 create a complex global patchwork of requirements. GDPR set the template, but dozens of countries and regions have implemented their own variations, each with unique requirements, definitions, and penalties.
Organizations operating internationally face simultaneous compliance with contradictory regulations. Requirements considered mandatory in one jurisdiction might be prohibited in another. Data residency laws require certain information remain within specific geographic boundaries while business operations demand cross-border data flows.
Consumer privacy expectations continue rising. Beyond regulatory compliance, organizations face reputational risks and customer defection if privacy practices don’t meet evolving standards. Privacy has become a competitive differentiator, not just a compliance obligation.
Privacy by Design and Default
Privacy engineering in 2026 integrates privacy considerations throughout system design and development rather than bolting them on afterward. This “privacy by design” approach includes:
- Data minimization: Collecting only necessary information and retaining it no longer than required
- Purpose limitation: Using data only for specifically disclosed purposes
- Privacy-enhancing technologies: Implementing encryption, anonymization, and differential privacy to protect data throughout its lifecycle
- User control: Providing meaningful consent mechanisms and easy access to personal data
- Transparent practices: Clearly communicating what data is collected, why, and how it’s used
Automated privacy management platforms handle the complexity of multi-jurisdiction compliance, mapping data flows, managing consent, responding to data subject requests, and generating required documentation.
Organizations treating privacy as a checkbox compliance exercise face exponentially increasing regulatory penalties and customer exodus. Those embracing privacy as fundamental to operations build trust and competitive advantages.
Cloud Security Challenges Intensify
Multi-Cloud and Hybrid Complexity
Multi-cloud environments—using services from AWS, Azure, Google Cloud, and others simultaneously—create security challenges that traditional approaches can’t address. Each platform has unique security controls, configurations, and best practices.
Misconfigurations remain the leading cause of cloud breaches in 2026. A single incorrectly configured storage bucket exposes millions of records. The complexity of cloud platforms combined with rapid deployment cycles creates countless opportunities for dangerous mistakes.
Shared responsibility confusion leads to serious gaps. Cloud providers secure the infrastructure; customers secure everything running on it. Many organizations misunderstand where their responsibilities begin, leaving critical security controls unimplemented.
Cloud-Native Security Solutions
Cloud security posture management (CSPM) tools continuously scan cloud environments, identifying misconfigurations, compliance violations, and security risks. These automated systems provide the visibility and control necessary for complex multi-cloud environments.
Container security becomes critical as containerized applications proliferate. Securing containers requires protecting images, runtime environments, and orchestration platforms like Kubernetes throughout development and production lifecycles.
Infrastructure as code (IaC) security scans configuration templates before deployment, catching security issues in development rather than production. This shift-left approach prevents misconfigurations from ever reaching live environments.
Organizations succeeding in cloud security recognize that traditional perimeter-based approaches don’t translate to cloud environments. Cloud-native security requires cloud-native tools, practices, and mindsets.
The Cybersecurity Skills Crisis Deepens
Automation as Partial Solution
The cybersecurity talent shortage reaches crisis levels in 2026, with demand far exceeding supply. Organizations can’t simply hire their way to security when qualified candidates don’t exist in sufficient numbers.
Security automation and AI-assisted security operations help bridge the gap. Automated systems handle repetitive tasks—log analysis, threat detection, initial incident triage—allowing human experts to focus on complex decision-making and strategic initiatives.
Security orchestration, automation, and response (SOAR) platforms coordinate multiple security tools, automatically execute response playbooks, and significantly multiply the effectiveness of small security teams.
Alternative Talent Development
Organizations are developing internal talent through training programs, mentorship, and career progression paths. Converting IT professionals into security specialists proves more practical than competing for scarce experienced security experts.
Managed security service providers (MSSPs) enable smaller organizations to access enterprise-grade security expertise they couldn’t hire directly. These services provide 24/7 monitoring, threat detection, and incident response without building internal security operations centers.
The successful organizations of 2026 recognize that perfect security with unlimited resources is fantasy. They optimize security programs within real-world constraints, using automation and managed services strategically while developing internal capabilities over time.
Insider Threats Grow More Sophisticated
Beyond Malicious Employees
Insider threats in 2026 extend far beyond disgruntled employees stealing data. The category includes negligent users making dangerous mistakes, compromised credentials, and social engineering that tricks authorized users into granting access.
Privileged access abuse represents particularly dangerous insider risk. Users with administrative privileges, database access, or system control can bypass many security controls. Whether through malicious intent or account compromise, privileged user actions create severe damage.
Data exfiltration by departing employees has become commonplace. Workers changing jobs copy customer lists, intellectual property, and business strategies to their new employers. The boundary between appropriate knowledge transfer and theft has blurred dangerously.
Behavioral Analytics and Access Controls
User and entity behavior analytics (UEBA) establish baselines of normal activity for each user and system. Deviations trigger alerts or automatic restrictions before significant damage occurs.
Just-in-time access grants elevated privileges only when needed for specific tasks and automatically revokes them afterward. This approach dramatically reduces the window during which compromised accounts or malicious insiders can abuse privileges.
Data loss prevention (DLP) tools monitor and control sensitive information movement. These systems prevent bulk data exports, flag suspicious access patterns, and encrypt sensitive files automatically.
Organizations recognizing that trusted insiders pose risks comparable to external attackers implement appropriate monitoring and controls without creating oppressive or distrustful work environments.
Conclusion
The cybersecurity landscape of 2026 is simultaneously more dangerous and more manageable than ever before. Threats have grown in sophistication, scale, and impact, but defensive capabilities have advanced equally impressively for organizations willing to invest appropriately.
The common thread connecting every trend discussed—AI-powered attacks, quantum computing threats, ransomware evolution, supply chain risks, privacy regulations, cloud security challenges, talent shortages, and insider threats—is that reactive, checkbox approaches to security no longer work. Organizations succeeding in 2026 treat cybersecurity as continuous, strategic, and integrated throughout business operations.
You don’t need to address every trend simultaneously. Start by honestly assessing your organization’s specific risks, current security posture, and available resources. Prioritize the threats most likely to impact your specific environment and implement foundational controls before pursuing advanced capabilities.
The cybersecurity challenges of 2026 are formidable, but they’re not insurmountable. Organizations that act now—implementing zero trust architecture, preparing for quantum threats, addressing talent gaps strategically, and adopting AI-powered defenses—will thrive. Those that wait until crises force action will find themselves fighting yesterday’s battles with yesterday’s tools while facing tomorrow’s threats.
The question isn’t whether cyber threats will continue evolving—they will. The question is whether you’ll be ready when they arrive at your doorstep. Start preparing today.
Frequently Asked Questions
What’s the single most important cybersecurity investment organizations should make in 2026?
While comprehensive security requires multiple investments, implementing zero trust architecture provides the highest return across the widest range of threats. Zero trust fundamentally changes how organizations approach security, addressing insider threats, compromised credentials, lateral movement, and cloud security simultaneously. It’s not the easiest or cheapest investment, but it’s the most transformative. Organizations should begin with identity and access management, then gradually extend zero trust principles across their entire environment over 12-18 months.
How worried should small businesses be about quantum computing threats?
Small businesses should begin awareness and planning now but don’t need to panic immediately. Quantum computers capable of breaking current encryption are likely 3-7 years away from practical use by adversaries. However, “harvest now, decrypt later” attacks mean sensitive data with long-term value is at risk today. Small businesses should inventory cryptographic implementations, follow NIST post-quantum cryptography standards, and ensure vendors and critical systems have migration plans. The key is gradual preparation, not emergency response, while prioritizing other more immediate threats like ransomware and phishing.
Are AI-powered cyberattacks really as dangerous as this article suggests?
Yes, and potentially more so. AI has fundamentally changed the economics and scale of cyberattacks. Tasks that previously required specialized expertise and weeks of effort now happen automatically in minutes. AI enables mass personalization of attacks, allowing criminals to target thousands of victims with individualized, highly convincing phishing campaigns simultaneously. Deepfakes bypass authentication methods organizations trust. Polymorphic malware evades traditional defenses. The good news: AI-powered defense tools have advanced similarly, providing detection and response capabilities impossible with manual approaches. Organizations must adopt AI defensively or face insurmountable disadvantages against AI-armed attackers.
How can organizations address cybersecurity with severe talent shortages?
Organizations should embrace a multi-faceted strategy combining automation, managed services, and internal development. Security automation handles repetitive tasks, multiplying the effectiveness of small teams. Managed security service providers deliver expertise smaller organizations can’t hire directly. Cross-training existing IT staff into security roles develops internal capabilities over time. Simplifying security architectures through consolidation reduces management complexity. Most importantly, organizations must accept that perfect security with unlimited experts isn’t achievable—prioritization based on actual risk becomes critical. The most successful organizations optimize security within real-world constraints rather than pursuing unattainable ideals.